 ‘Tis the season for technology vulnerabilities and exploits. In addition to Sandworm and Cryptowall 2.0, another flaw has been found in Microsoft Office. This particular threat allows a hacker to gain control of a computer system, making it a dangerous and potentially threatening gamble for your business to ignore it. Thankfully, the issue has been patched, and the fix is now available to the public.
‘Tis the season for technology vulnerabilities and exploits. In addition to Sandworm and Cryptowall 2.0, another flaw has been found in Microsoft Office. This particular threat allows a hacker to gain control of a computer system, making it a dangerous and potentially threatening gamble for your business to ignore it. Thankfully, the issue has been patched, and the fix is now available to the public.
Microsoft issued a security advisory on October 21st stating that the vulnerability, which allows remote code execution, is found in all supported versions of Microsoft Windows, excluding Windows Server 2003. The threat is triggered by opening an infected Microsoft Office file which contains an OLE (Object Linking and Embedding) object. If the hacker is successful, they can potentially gain the same user rights as other users on the PC, making it a very dangerous vulnerability indeed. If hackers are able to access the system, they can delete data, install malware, or other malicious activity.
The patch for this vulnerability was issued earlier this November, so if you still haven’t patched your systems from this threat, it’s important that you do so as soon as possible.
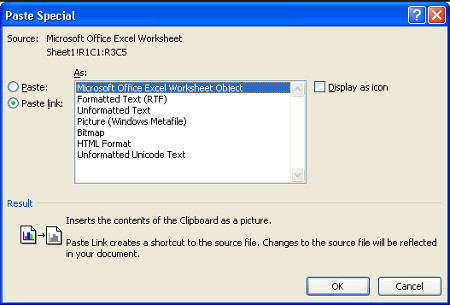
Thankfully, the vulnerability requires security permission from whoever has the administrative privileges on your business’s PCs. This means that if you were to download an Office file from the web, a window will appear asking if you are sure you want to download it. An example of Object Linking and Embedding (OLE) is embedding an Excel spreadsheet in a Word document.
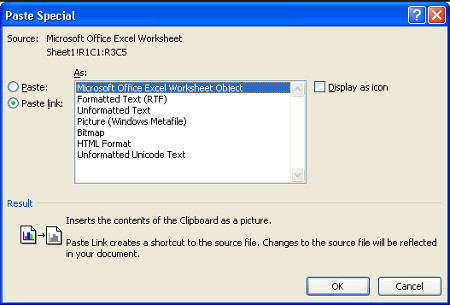
Officially, Microsoft says that any Office file utilizing an OLE object is vulnerable to being infected with this threat. Here are some tips you can use to protect yourself until you apply the security update.
- Enable the Windows Consent Prompt: In the observed attacks, the User Control Account interface displays a window with a consent prompt. This appears depending on the privileges of the current user, before the file can be downloaded. Make sure that this feature is enabled, as it can prevent you from downloading infected files before it’s too late.
- Enable fewer user rights on your systems: The hacker who infiltrates your system will gain the same usage rights as the currently logged-in user. This means that the more user rights they have, the more damage they can do. Either way, the average employee shouldn’t have administrative user rights, as it could lead to them performing unapproved tasks, like downloading unnecessary software and such.
- Avoid email phishing attacks: In theory, a hacker could convince an unaware user to visit an infected web page which could contain a vulnerable office file. They will typically do this by using links in malicious emails. Keep an eye out for suspicious activity, and never click on a link unless you know where it goes.
- Avoid downloading files from the Internet in general: Files from the web can contain any number of worms, viruses, malware, adware or other malicious entities you want nowhere near your network.
As always, it’s important that you apply the latest security updates as they are released. Business Solutions & Software Group can take care of this for you remotely and efficiently, so you don’t have to take the time to do so yourself.
In the face of tough threats such as this one, it’s best to equip your business with a comprehensive security solution, like Business Solutions & Software Group’s Unified Threat Management device (UTM). With a UTM, you can rest easy knowing that your network is protected by powerful firewalls, antivirus, web content filtering and spam protection solutions designed to keep the threats out. For more information about how to integrate a UTM device into your business’s security plans, give Business Solutions & Software Group a call at (954) 575-3992.

Comments